Network Registry Overview About 41.62×24 and System Records

The Network Registry Overview for 41.62×24 and System Records presents a governance-driven catalog of identifiers, routes, and access controls across devices and domains. It links system IDs to network segments, fingerprint data, and connectivity status to support precise RBAC auditing. This structured mapping enables reproducible troubleshooting, timestamped changes, and auditable lineage. The approach scales policy enforcement and accountability, but practical implications and workflows warrant careful examination to ensure robust implementation and ongoing justification.
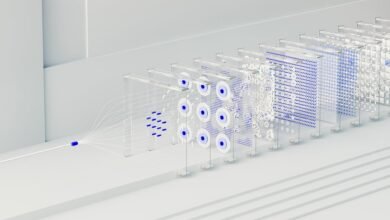
What Is the Network Registry 41.62×24 and Why It Matters?
The Network Registry 41.62×24 is a centralized system that catalogs and coordinates network identifiers, resources, and configuration records across connected devices and domains. It enables Networking mapping, supports Registry integrity, and preserves System records for auditability. Device mapping aligns assets with policies, while Compliance auditing verifies adherence to standards. Clear governance ensures scalable, interoperable, freedom-oriented network administration without ambiguity.
How System Records Map Devices, Routes, and Permissions
How do System Records map devices, routes, and permissions within the Network Registry 41.62×24? System Records perform structured indexing, linking device identifiers to network segments, route tables, and access controls.
They support device mapping by cataloging hardware, software fingerprints, and connectivity status.
Permission auditing ensures role-based access is recorded, reviewed, and reconciled, strengthening governance and traceability across the registry.
Practical Workflows for Troubleshooting and Auditing
Practical workflows for troubleshooting and auditing within the Network Registry 41.62×24 establish a disciplined sequence of diagnostic checks and evidence collection. The approach emphasizes reproducible procedures, labeled artifacts, and traceable timestamps. It defines concrete steps for discovery, hypothesis testing, and documentation. Through structured auditing, stakeholders understand network registry integrity, enabling efficient troubleshooting while preserving freedom to adapt methods to evolving technical contexts.
Security, Compliance, and Scalability Benefits of Precise Registry Data
Precise registry data enhances security, compliance, and scalability by enabling deterministic access control, verifiable auditing trails, and scalable policy enforcement across network registries.
This approach supports risk assessment by clarifying exposure and responsibilities, while data lineage maintains traceability of changes and rationale.
Quantified visibility enables consistent governance, reduces ambiguity, and promotes scalable enforcement without sacrificing flexibility for freedom-oriented architectures.
Conclusion
The Network Registry 41.62×24 and System Records synthesize structured, scalable stewardship of system identifiers, routes, and access controls. Precise provenance promotes reproducible troubleshooting, rigorous RBAC auditing, and verifiable change histories. By methodically mapping devices, fingerprints, and connectivity, stakeholders strengthen security, compliance, and accountability. This disciplined data discipline delivers dependable diagnostics, durable documentation, and decisive decisions, driving disciplined deployment and diligent defense across diverse domains.