Call Monitoring Documentation About 8007025d and Activity Logs

Call Monitoring documentation for 8007025d and activity logs must clearly define the meaning of authentication failures, their causes (expired credentials, invalid tokens), and their impact on data capture. It should specify traceable timestamps, user and system context, and consistent terminology. Logs require verification steps, access scopes, and reestablishment actions, all under immutable references and versioned templates. Governance, retention, and review cycles must be established, with reproducible workflows to sustain audit readiness and ongoing process improvement.
What 8007025d Means for Call Monitoring
The error code 8007025d indicates a failed or incomplete authentication attempt during call monitoring, typically arising from expired credentials, invalid tokens, or mismatched security context.
This condition disrupts data capture and alerting, prompting credential refresh, token validation, and context reestablishment.
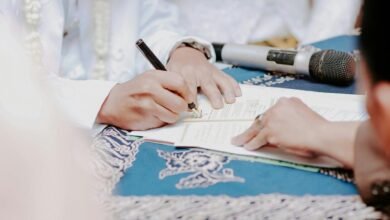
In practice, investigators document 8007025d meaning occurrences, verify access scopes, and ensure consistent monitoring configurations for reliable call monitoring outcomes.
Structuring Activity Logs for Compliance and Training
Effective structuring of activity logs is required to support both compliance audits and investigator training. Logs should be organized by event type, timestamp, user, and system context to enable quick cross-checks and lawful review. Ensure consistent terminology, immutable references, and versioned templates. Focus on compliance alignment and training effectiveness, enabling auditors and trainers to verify processes without ambiguity. Documentation integrity remains paramount.
Capturing the Right Data: Metrics, Metadata, and Standards
How should one capture data to ensure reliable audits and training relevance? The protocol defines targeted data capture: define clarity metrics, record event timestamps, and annotate calls with privacy metadata. Standardized formats enable consistent sampling, traceability, and reproduce audits. Metadata should reflect purpose, access controls, and retention. Regular reviews confirm alignment with standards, minimizing ambiguity while preserving practical freedom in analysis and training relevance.
Best Practices for Storage, Review, and Continuous Improvement
Storage and review practices must establish reliable preservation, access control, and reproducible workflows to support audits and ongoing improvement.
The procedure defines formal call monitoring governance, roles, and responsibilities, with documented retention timelines and review cycles.
Data retention policies align with regulatory expectations, ensuring traceability, non-repudiation, and timely disposal.
Regular audits, metrics, and continuous improvement loops drive transparent, auditable, freedom-respecting governance.
Conclusion
The documentation framework for 8007025d and activity logs is a locked ledger: precise, immutable, and auditable. It uses standardized terminology, traceable timestamps, and clearly defined failure causes to illuminate authentication events and their data-capture impact. Like a compass, verification steps and access scopes orient investigations; reestablishment efforts restore continuity. As in a well-kept archive, governance, retention, and review cycles ensure ongoing integrity and readiness, with reproducible workflows guiding continual improvement and audit-facing training.